- 27 Posts
- 29 Comments

 3·2 days ago
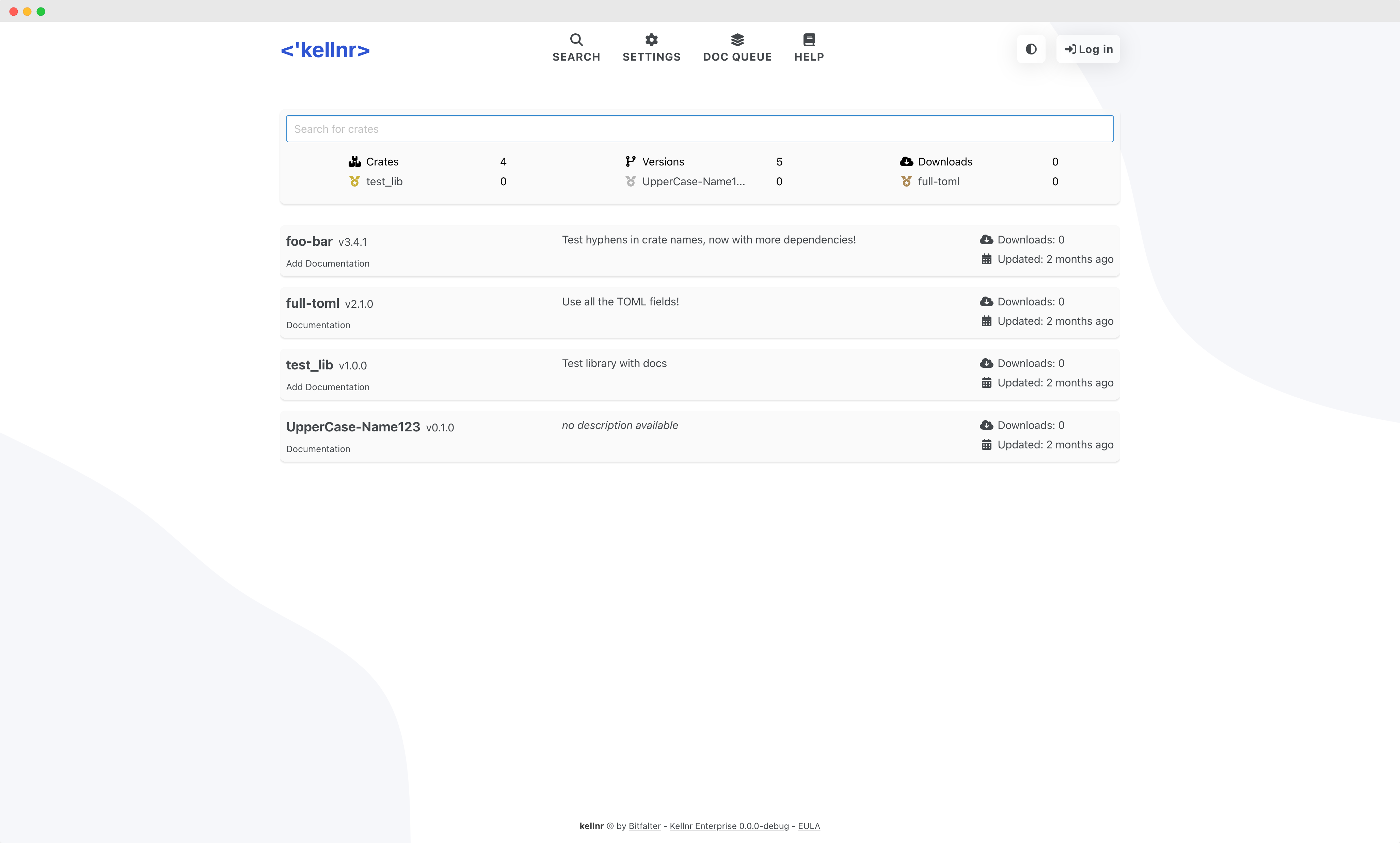
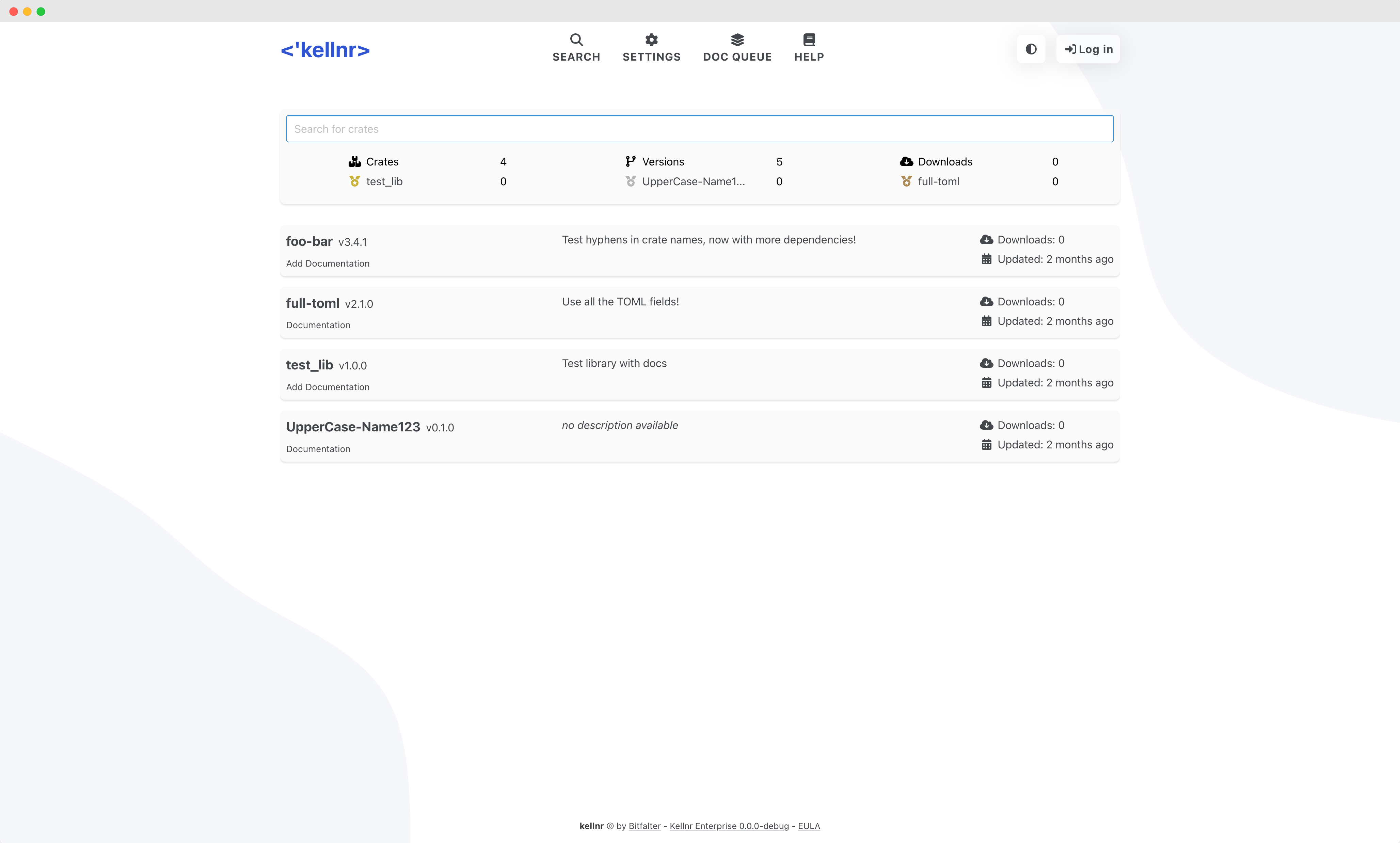
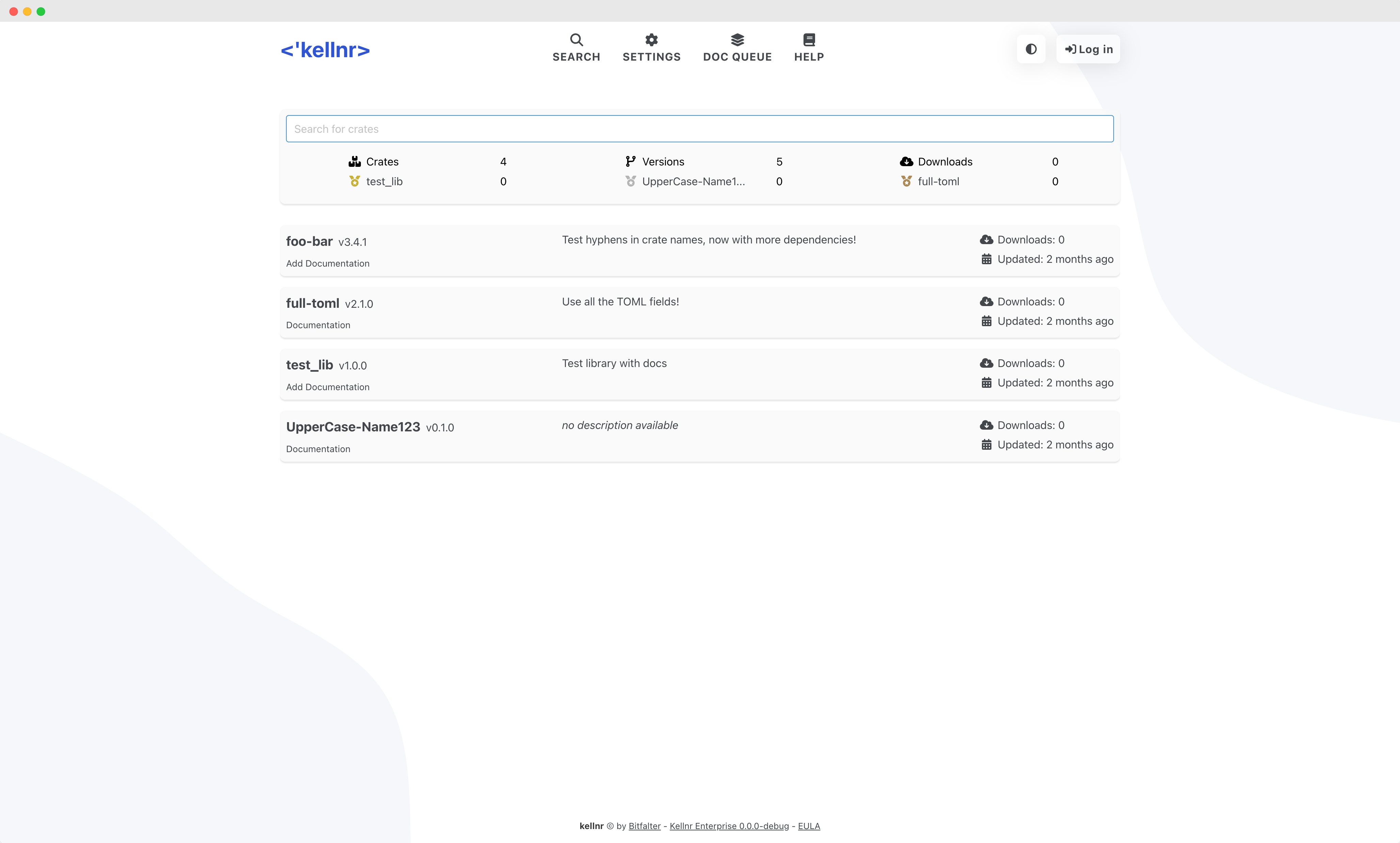
3·2 days agoJust released Kellnr (https://kellnr.io) 5.2.6 with some bug fixes. I really wish I had more time for new features but at the moment my spare time is rare. If you want to host your own crates on your own infrastructure, check it out.

 2·1 month ago
2·1 month agoThanks, I’ll try that!

 2·1 month ago
2·1 month agoSure. I import the certificates like this:
{ config, pkgs, inputs, ... }: { security.pki.certificateFiles = [ ./certificates/home.pem ]; }where
home.pemis a default PEM formatted certificate. It works fine to import the cert system wide this way.If I enter the flake.nix and run a simple
curlagainst the remote server I get the following, which is typical for a TLS certificate error.curl https://webpage.home curl: (35) OpenSSL/3.0.14: error:16000069:STORE routines::unregistered schemeSo it seems to me that the development shell does not pick up the certificates installed on the system. I can work around that by using an impure shell, but I think that this is not how nix should be used.

 2·2 months ago
2·2 months agoThanks for the response. You are right, the config was at the wrong path. Unfortunately, the config itself does not work, too. After a bit of testing around this worked for me:
apiVersion: v1 kind: PersistentVolume metadata: name: nix-cache-volume spec: capacity: storage: 500Gi storageClassName: manual accessModes: - ReadWriteOnce hostPath: path: "/mnt/k8s/nix-cache" # Needs exists before PV is created! persistentVolumeReclaimPolicy: Retain --- apiVersion: v1 kind: PersistentVolumeClaim metadata: name: nix-cache-pvc spec: accessModes: - ReadWriteOnce storageClassName: manual resources: requests: storage: 500Gi --- apiVersion: apps/v1 kind: Deployment metadata: name: nix-cache spec: replicas: 1 selector: matchLabels: app: nix-cache template: metadata: labels: app: nix-cache name: nix-cache spec: volumes: - name: nix-cache-storage persistentVolumeClaim: claimName: nix-cache-pvc - name: nix-cache-config configMap: name: nix-cache-config containers: - name: nix-cache image: nginx:1.27.0 ports: - containerPort: 80 volumeMounts: - name: nix-cache-storage mountPath: /data - name: nix-cache-config mountPath: /etc/nginx/nginx.conf subPath: nginx.conf readOnly: true resources: limits: memory: "512Mi" cpu: "300m" requests: memory: "256Mi" cpu: "200m" --- apiVersion: v1 kind: Service metadata: name: nix-cache spec: selector: app: nix-cache ports: - protocol: TCP port: 80 targetPort: 80 --- apiVersion: networking.k8s.io/v1 kind: Ingress metadata: name: nix-cache-ingress annotations: traefik.ingress.kubernetes.io/router.tls: "true" spec: rules: - host: "nix-cache.raspi.home" http: paths: - pathType: Prefix path: "/" backend: service: name: nix-cache port: number: 80 tls: - secretName: nix-cache-raspi-home-tls hosts: - "nix-cache.raspi.home" --- apiVersion: cert-manager.io/v1 kind: Certificate metadata: name: nix-cache.raspi.home spec: commonName: nix-cache.raspi.home dnsNames: - "nix-cache.raspi.home" secretName: nix-cache-raspi-home-tls issuerRef: name: ca-issuer kind: ClusterIssuer --- apiVersion: v1 kind: ConfigMap metadata: name: nix-cache-config data: # See: https://www.channable.com/tech/setting-up-a-private-nix-cache-for-fun-and-profit nginx.conf: | events { worker_connections 1024; } http { proxy_cache_path /data/nginx/cache max_size=500G keys_zone=cache_zone:50m inactive=365d; proxy_cache cache_zone; proxy_cache_valid 200 365d; proxy_cache_use_stale error timeout invalid_header updating http_500 http_502 http_504 http_403 http_404 http_429; proxy_ignore_headers X-Accel-Expires Expires Cache-Control Set-Cookie; proxy_cache_lock on; server { listen 80; server_name nix-cache.raspi.home; location /nix-cache-info { return 200 "StoreDir: /nix/store\nWantMassQuery: 1\nPriority: 41\n"; } location / { proxy_set_header Host $proxy_host; proxy_pass https://cache.nixos.org; } } }The config is an adaption from this blog post: https://www.channable.com/tech/setting-up-a-private-nix-cache-for-fun-and-profit

 95·6 months ago
95·6 months agohttps://tauri.app/ is very popular and does not need electron. It uses the OS native we view.

 9·6 months ago
9·6 months agoThe runtime is even called “common language runtime” (clr), as it is intended to support many different languages, which the jvm never was.

 3·6 months ago
3·6 months agoThanks! Took me few iterations to get there.

 12·6 months ago
12·6 months agoI released https://kellnr.io 5.2.1 with a few smaller fixes and additions.

 10·7 months ago
10·7 months agoIf that really works without any drawbacks, I hope it gets merged into Rust main.

 4·7 months ago
4·7 months agoI released the next minor version of https://kellnr.io which support the display of crates, cached from crates.io, in the UI now. For the first iteration of that feature, they are only shown and searchable in the crate overview and a click forwards to crates.io, as not all meta information is stored in kellnr, for cached crates. That may change in the future, if someone requests it.

 4·7 months ago
4·7 months agoYeah, real world duties have priority over programming rust. Unfortunately.
Happy to hear that it worked!
The Windows linker needs a lib file to link a DLL. See here how it’s done https://kellnr.io/blog/cross-plat-native-lib

 2·7 months ago
2·7 months agoThat’s one of the best programming books I’ve read. How do you like rust so far?

 2·7 months ago
2·7 months agoNever heard of them. Kellnr is already three years old. It started when only git was supported as the registry protocol. I later added the sparse (http) registry API. Just a few weeks ago, I removed the old git API, as sparse seems established as the new standard. I never thought about namespacing, as Kellnr is aimed as private hosting for individuals or companies, where name squatting isn’t an issue. But theoretically, I could add that.

 2·7 months ago
2·7 months agoCool! What’s your impression of typst? Is it ready to replace latex or is it still in its infancy?

 3·7 months ago
3·7 months agoHow easy is it to create custom widgets with iced.rs? Or does Cosmic provide it’s own full widget library?

 6·7 months ago
6·7 months agoI started to implement a new feature for https://kellnr.io. Currently, only private crates are displayed in the UI, but the users wished for the possibility to display cached crates from crates.io, as well. Hopefully a new version will be out in the next days, with the new feature.

 1·7 months ago
1·7 months agoDone. I’m using KDE since 20 years. Keep up the good work!
An honorable goal 😀